Security researchers have discovered a way to target a huge number of Android and iOS apps that could allow them to remotely sign into any victim's mobile app account without any knowledge of the victim.
A group of three researchers – Ronghai Yang, Wing Cheong Lau, and Tianyu Liu – from the Chinese University of Hong Kong has found [PPT] that most of the popular mobile apps that support single sign-on (SSO) service have insecurely implemented OAuth 2.0.
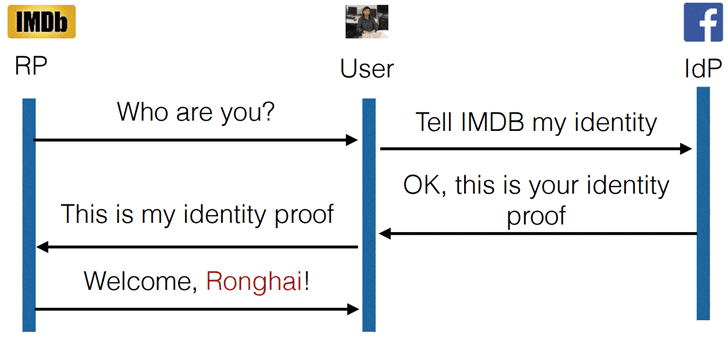
OAuth 2.0 is an open standard for authorization that allows users to sign in for other third-party services by verifying existing identity of their Google, Facebook, or Chinese firm Sina accounts.
This process enables users to sign-in to any service without providing additional usernames or passwords.
Once access token is issued, the app server asks for the user's authentication information from Facebook, verify it and then let the user login with his/her Facebook credentials.
Instead of verifying OAuth information (Access Token) attached to the user's authentication information to validate if the user and ID provider are linked, the app server would only check for user ID retrieved from the ID provider.
Due to this blunder, remote hackers can download the vulnerable app, log in with their own information and then change their username to the individual they want to target (which the hackers could guess or Google) by setting up a server to modify the data sent from Facebook, Google or other ID providers.
Once done, this would grant the snoop total control of the data held within the app, reports Forbes.
The impact? If hackers broke into a victim's travel app, they could learn the schedules of the victim; if broke into a hotel booking app, they could book a room for them and have the victim pay; or simply steal victim's personal data, such as residential address or bank details.
Considering the number of users who opt for OAuth-based logins, researchers estimate that over a Billion different mobile app accounts are at risk of being hijacked with their attack.
The researchers did not test their exploits on iPhones, but they believed that their attack would work on any vulnerable app sitting on Apple's iOS mobile operating system.
"Although our current attack is demonstrated over the Android platform, the exploit itself is platform-agnostic: any iOS or Android user of the vulnerable mobile app is affected as long as he/ she has used the OAuth2.0-based SSO service with the app before," the researchers said.
Yang and Lau presented their research paper titled, Signing into One Billion Mobile App Accounts Effortlessly with OAuth2.0, at Black Hat Europe conference on Friday.
A group of three researchers – Ronghai Yang, Wing Cheong Lau, and Tianyu Liu – from the Chinese University of Hong Kong has found [PPT] that most of the popular mobile apps that support single sign-on (SSO) service have insecurely implemented OAuth 2.0.
OAuth 2.0 is an open standard for authorization that allows users to sign in for other third-party services by verifying existing identity of their Google, Facebook, or Chinese firm Sina accounts.
This process enables users to sign-in to any service without providing additional usernames or passwords.
How are app developers required to implement OAuth? (Right Way)
When a user logs into a third party app via OAuth, the app checks with the ID provider, let's say, Facebook, that it has correct authentication details. If it does, OAuth will have an 'Access Token' from Facebook which is then issued to the server of that mobile app.Once access token is issued, the app server asks for the user's authentication information from Facebook, verify it and then let the user login with his/her Facebook credentials.
How are app developers actually implementing OAuth? (Wrong Way)
Researchers found that the developers of a massive number of Android apps did not properly check the validity of the information sent from the ID provider, like Facebook, Google or Sina.Instead of verifying OAuth information (Access Token) attached to the user's authentication information to validate if the user and ID provider are linked, the app server would only check for user ID retrieved from the ID provider.
Due to this blunder, remote hackers can download the vulnerable app, log in with their own information and then change their username to the individual they want to target (which the hackers could guess or Google) by setting up a server to modify the data sent from Facebook, Google or other ID providers.
Once done, this would grant the snoop total control of the data held within the app, reports Forbes.
The impact? If hackers broke into a victim's travel app, they could learn the schedules of the victim; if broke into a hotel booking app, they could book a room for them and have the victim pay; or simply steal victim's personal data, such as residential address or bank details.
"The OAuth protocol is quite complicated," Lau told Forbes. "A lot of third party developers are ma and pa shops, they don't have the capability. Most of the time they're using Google and Facebook recommendations, but if they don't do it correctly, their apps will be wide open."The researchers have found hundreds of popular US and Chinese Android apps that support SSO service with a total of over 2.4 Billion downloads that are vulnerable to this issue.
Considering the number of users who opt for OAuth-based logins, researchers estimate that over a Billion different mobile app accounts are at risk of being hijacked with their attack.
The researchers did not test their exploits on iPhones, but they believed that their attack would work on any vulnerable app sitting on Apple's iOS mobile operating system.
"Although our current attack is demonstrated over the Android platform, the exploit itself is platform-agnostic: any iOS or Android user of the vulnerable mobile app is affected as long as he/ she has used the OAuth2.0-based SSO service with the app before," the researchers said.
Yang and Lau presented their research paper titled, Signing into One Billion Mobile App Accounts Effortlessly with OAuth2.0, at Black Hat Europe conference on Friday.
Have something to say about this article? Comment below or share it with us on Facebook, Twitter or our LinkedIn Group.