A security researcher has revealed details of a new piece of undetectable malware targeting Apple's Mac computers—reportedly first macOS malware of 2018.
Dubbed OSX/MaMi, an unsigned Mach-O 64-bit executable, the malware is somewhat similar to DNSChanger malware that infected millions of computers across the world in 2012.
DNSChanger malware typically changes DNS server settings on infected computers, allowing attackers to route internet traffic through malicious servers and intercept sensitive information.
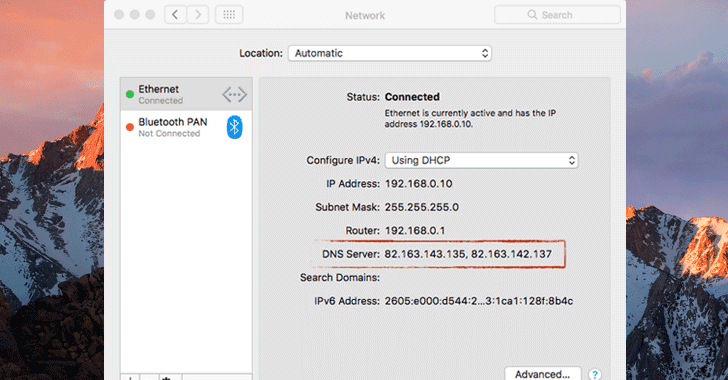
First appeared on the Malwarebytes forum, a user posted a query regarding unknown malware that infected his friend's computer that silently changed DNS settings on infected macOS to 82.163.143.135 and 82.163.142.137 addresses.
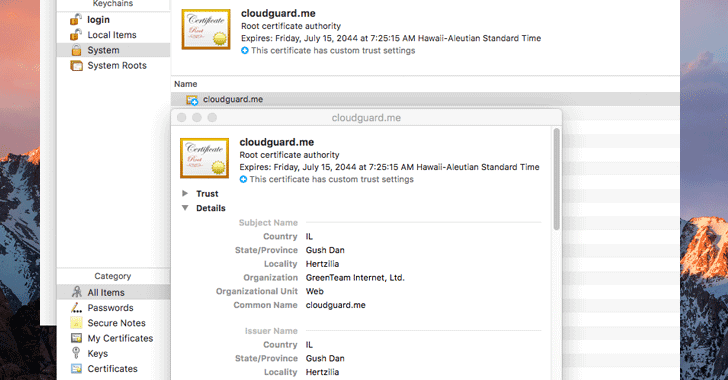
After looking at the post, ex-NSA hacker Patrick Wardle analysed the malware and found that it is indeed a 'DNS Hijacker,' which also invokes security tools to install a new root certificate in an attempt to intercept encrypted communications as well.
However, Patrick believes that the attackers could be using lame methods like malicious emails, web-based fake security alerts/popups, or social-engineering type attacks to target Mac users.
To check if your Mac computer is infected with MaMi malware, go to the terminal via the System Preferences app and check for your DNS settings—particularly look for 82.163.143.135 and 82.163.142.137.
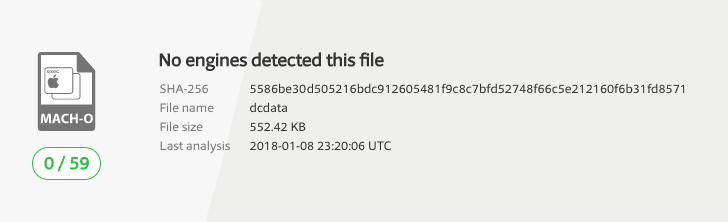
According to VirusTotal, a multi-engine antivirus scanner, none of 59 popular antivirus software is detecting this malware at this moment, so you are advised to use a 3rd-party tool such as a firewall that can detect and block outgoing traffic.
You can also install a free open-source firewall for macOS named 'LuLu,' created by Patrick and available at GitHub, which blocks suspicious traffic and prevents OSX/MaMi's from stealing your data.
Dubbed OSX/MaMi, an unsigned Mach-O 64-bit executable, the malware is somewhat similar to DNSChanger malware that infected millions of computers across the world in 2012.
DNSChanger malware typically changes DNS server settings on infected computers, allowing attackers to route internet traffic through malicious servers and intercept sensitive information.
First appeared on the Malwarebytes forum, a user posted a query regarding unknown malware that infected his friend's computer that silently changed DNS settings on infected macOS to 82.163.143.135 and 82.163.142.137 addresses.
After looking at the post, ex-NSA hacker Patrick Wardle analysed the malware and found that it is indeed a 'DNS Hijacker,' which also invokes security tools to install a new root certificate in an attempt to intercept encrypted communications as well.
"OSX/MaMi isn't particularly advanced - but does alter infected systems in rather nasty and persistent ways," Patrick said.
"By installing a new root certificate and hijacking the DNS servers, the attackers can perform a variety of nefarious actions such as man-in-the-middle'ing traffic (perhaps to steal credentials, or inject ads)" or to insert cryptocurrency mining scripts into web pages.Besides this, the OSX/MaMi macOS malware, which appears to be in its initial stage, also includes below-mentioned abilities, most of which are not currently activated in its version 1.1.0:
- Take screenshots
- Generate simulated mouse events
- Perhaps persist as a launch item
- Download and upload files
- Execute commands
The motive, author(s) behind the malware, and how it is spreading are currently unknown.
However, Patrick believes that the attackers could be using lame methods like malicious emails, web-based fake security alerts/popups, or social-engineering type attacks to target Mac users.
To check if your Mac computer is infected with MaMi malware, go to the terminal via the System Preferences app and check for your DNS settings—particularly look for 82.163.143.135 and 82.163.142.137.
According to VirusTotal, a multi-engine antivirus scanner, none of 59 popular antivirus software is detecting this malware at this moment, so you are advised to use a 3rd-party tool such as a firewall that can detect and block outgoing traffic.
You can also install a free open-source firewall for macOS named 'LuLu,' created by Patrick and available at GitHub, which blocks suspicious traffic and prevents OSX/MaMi's from stealing your data.
Have something to say about this article? Comment below or share it with us on Facebook, Twitter or our LinkedIn Group.